Educator’s Guide: Types of Online Fakes
Written by Craig Silverman and Rina Tsubaki
The misinformation and hoaxes that flow over the Internet often fall into specific categories. Understanding what to expect can help you make the right call in a fast moving situation, and avoid giving a hoax new life.
The types of fakes fit into the following categories:
1. Real photos from unrelated events.
2. Art, ads, film and staged scenes.
3. Photoshopped images.
4. Fake accounts.
5. Altered manual retweets.
6. Fake tweets.
7. Fake websites.
1. Real photos from unrelated events
As seen during Hurricane Sandy and the Syrian conflict, images and video from past events are frequently reuploaded and reused on social networks.

During Hurricane Sandy, this photo went viral on Twitter. The original photo was published by the Wall Street Journal over a year earlier, on April 28, 2011. But this resharing of the image with a Sandy hashtag quickly attracted retweets and favorites.
Tip: Run a reverse image search to see whether there is an earlier version of the same image online.
Source: http://verificationhandbook.com/additionalmaterial/types-of-online-fakes.php

This photo was shared on social networks after the game between Brazil and Germany during the World Cup in 2014. The incident in the photo actually dates back to June 2013, when a number of protests took place ahead of the World Cup. This Reuters photo capturing the scene near the Mineirao Stadium in Belo Horizonte, Brazil that June was reused by @FootballCentre and was retweeted more than 10,000 times.
Tip: Professional photos may be misused in order to report new events. As with the earlier example, a fake can easily be spotted by running a reverse image search.
Source: http://www.bustle.com/articles/30930-fake-brazil-riot-photos-on-twitter-arent-from- tuesdays-world-cup-loss-to-germany
Another example is a photo that claimed to show Darren Wilson, the police officer who killed Michael Brown in Ferguson, Mo. in 2014. The photo went viral on Facebook and was shared tens of thousands times. The individual in the photo is not Wilson. It’s Jim McNeil, a motocross rider who died in 2011. The photo itself is from 2006, when McNeil was injured after a crash.

Tip: Identify who and what are captured in the photo and triangulate by comparing different sources, while of course performing a reverse image search.
Source: http://antiviral.gawker.com/supposed-photo-of-injured-darren-wilson-is-just-some- wh-1630576562

This photo appeared on Venezuelan state- owned broadcaster VTV’s programme “Con El Mazo Dando.” It claimed to be proof of weapons being used by General Angel Vivasthe during the Venezuelan uprising in early 2014.
Interestingly, the same photo was found on the website of a gun store.
Tip: Fakes may be used by the governments and state-owned media outlets to spread their political message and misinform the public.
Source : http://elpaisperfecto.blogspot.nl/2014/02/montaje-de-diosdado-cabello-24-02- 20114.html
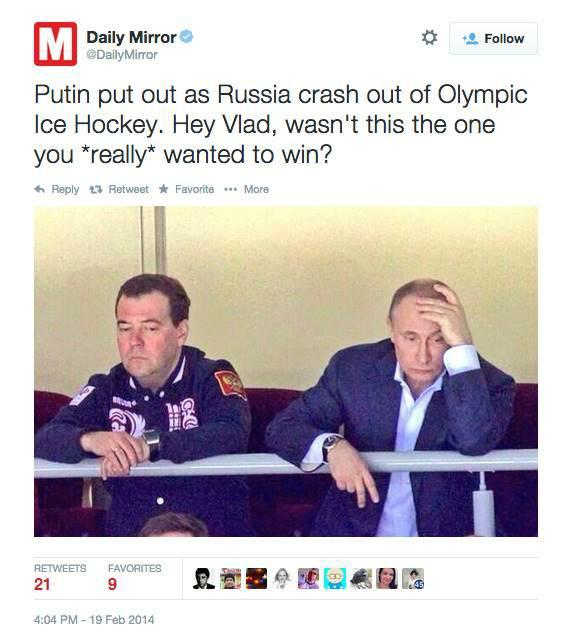
The Daily Mirror used this photo when the Russian Olympic hockey team was defeated by the Finnish team at the Sochi Winter Games in 2014. The photo was originally taken a few days earlier during the game between Russia and Slovakia — a game the Russians won.
Tip: It’s common practice for some media outlets to use a photo that best describes the story, rather than one from the actual event. It’s crucial to question whether images are from the actual event being described, especially on social media.
Source: https://www.politifact.com/factchecks/2014/feb/19/tweets/photo-showing-sad-/
When a ferry sank in South Korea, a FOX News report used old footage of the mother of a Mount Everest avalanche victim and portrayed it as being related to the ferry tragedy. The Korean Cultural Centre complained, as did other organizations.

Tip: Images being used to represent an event may reflect older footage, as well as poor sensitivity about races or ethnic groups. Don’t assume that the footage has been properly vetted.
This is another example where a photo from an unrelated event was used in a news story. On 27 May, 2012, the BBC reported about a massacre in Syria and used the above image. It included this description: “This image - which cannot be independently verified - is believed to show the bodies of children in Houla awaiting burial.” It was later identified as a photo from Iraq in 2003.
Tip: Pay close attention to photo descriptions that flag it as not having been fully verified.
2. Art, ads, movies and staged scenes
Users on social networks often circulate images taken from art, ads and films during real news events.

This tweet, sent during Hurricane Sandy, is actually a screen capture from an film art project entitled “Flooded McDonald’s,” which can be watched on Vimeo.
Tip: Be cautious of the images that are too good to be true, and seek out reliable sources to aid with confirmation. In this case, contacting local authorities to ask about the flooding situation in Virginia Beach could have provided some necessary context.
Source: http://www.snopes.com/photos/natural/sandy.asp

In January 2014, The Daily Bhaskar, a daily newspaper in India, used this photo in an article entitled “Heartbreaking pic: Syrian child sleeps between graves of his parents.” The photo, however, was part of art project by a Saudi Arabia-based photographer, and had been uploaded to Instagram weeks before this happened.
Tip: Media outlets do not necessary practice verification before sharing an image or other piece of content. It’sessential to perform your own verification before republishing.
Source: http://imediaethics.org/hoax-photo-of-syrian-boy-sleeping-between-parents-graves- was-staged/?new

This photo was posted across social networks with the hashtag #SaveDonbassPeople. However, it’s actually a still from the Russian war film, “The Brest Fortress.”
Tip: Check who’s spreading the photo. Are they politically active on one side or another, and have they shared other questionable images?
Source: http://www.stopfake.org/en/snapshot- of-movie-the-brest-fortress-is-being- presented-as-a-photo-of-donbass/
3. Photoshopped Images

This photo was released by North Korea’s state-owned Korean Central News Agency in March 2013. When The Atlantic examined the hovercrafts, they saw that they were identical to each other. The KCNA had cloned one hovercraft to make the image more threatening.
Tip: Handout images from governments, companies and other sources should be checked and verified.
Source: http://www.theatlantic.com/photo/2013/03/is-this-north-korean-hovercraft-landing-photo-faked/100480/

Prior to the Sochi Games in 2014, Quebec’s Minister of Higher Education, Research, Science and Technology came under attack after sharing a digitally manipulated photo of two athletes. The original photo did not include Quebec-branded gloves. After sending it, the minister deleted the tweet, adding “The perils of " photoshop " ... I am myself a victim. :)” His press attache also told the media that “He didn’t know before he tweeted it that the picture had been photoshopped.”
Tip: When influential people share images, they add a layer of credibility and virality to the content. But they too can be victims of fakes.
Source: http://globalnews.ca/news/1145676/quebec-minister-tweets-photoshopped- olympic-photo/

The Verification Handbook’s Case 4.2: Verifying Suspicious Sharks” During Hurricane Sandy explained how photoshopped shark images circulated during Hurricane Sandy. In fact, street sharks made an appearance even before Sandy. When Hurricane Irene struck in 2011, this tweet went viral, introducing many to the street shark phenomenon. The original photo of the shark is found in an issue of Africa Geographic in 2005.
Tip: Be very wary of shark images shared during hurricanes!
Source: https://www.imediaethics.org/7-fake-weather-photos-to-watch-out-for-in-the-2014-hurricane-season/

This example shows how traditional media outlets sometimes publish digitally manipulated photos. The Daily Mail published the image of Tottenham footballer Emmanuel Adebayor saluting the manager after his goal during the match between Tottenham and Sunderland. The print edition included a photo that erased Chris Ramsey, standing next to the manager
Tip: Professional photos published by media outlets are sometimes (though rarely) altered or manipulated. This is one of the recurring type of fakes that have existed throughout our history. Verification also needs to be applied to non-social media content.
4. Fake account

Fake accounts are a constant presence on social networks. They are usually set up using the names of celebrities, politicians or other famous people. This unverified account claimed to belong to the son of football player David Beckham and his popstar wife, Victoria Beckham. It was created in 2011 and gathered more than 27,000 followers, in spite of having many characteristics of fake accounts.
Tip: Twitter and Facebook verify accounts of famous/prominent people and organizations. You can spot these because they have a blue tick mark on the profile page. Second guess if there is no blue check mark, and ask them to share the evidence to authenticate the individual.
Source: https://alexirob.wordpress.com/2013/07/25/the-suspicious-account-of-brooklyn- beckham-brookbecks/

When Pope Francis I was appointed in 2013, a fake account, @JMBergoglio, tweeted "Immensely happy to be the new Pope, Francis I." Many people, including journalists, were fooled by this account, helping propel it to 100,000 followers within a few hours. However, a quick look at the account’s previous tweets reveals many questionable messages. This includes the above message which translates to, “If I'm the new pope, children will love me more than Santa Claus”.
Tip: Check previous tweets to see if they are consistent with the person.
Source: http://mashable.com/2013/03/13/new-pope-fake-twitter/

This Morrissey Twitter account is a unique example because it’s a case where Twitter itself wrongly verified a fake account.
Tip: While this is a rare case, this example shows that even a verified check cannot be treated as 100 percent reliable. Also remember that Twitter accounts can be hacked. In those cases, it’s not the real person tweeting.
Source: http://www.theverge.com/2014/5/19/5730542/morrissey-impersonated-on-twitter
5. Manual retweets

In 2009 Twitter introduced a retweet button that allows people to retweet the original tweet on their feed. However, many users still manually retweet by copy- pasting the original tweet with RT at the beginning. This opens up the possibility that people will alter the original message and attribute it to other users. It also means that previously deleted messages can live on as manual retweets, thereby spreading misinformation.
Tip: Check if you can find the original tweet.
6. Fake tweet, facebook wall posts and iPhone conversations
There are a number of tools and apps that allow people to easily create a fake tweets, Facebook wall posts and iPhone conversations. Here’s a look at some of the ones to watch out for.
- The Wall Machine (http://thewallmachine.com/):
This tool can be used to create fake Facebook wall posts. After signing in with your Facebook account, you can create a profile photo, account name and comments on your imaginary post. A similar tool is from Simulator.com, where you can create a fake Facebook post and download the JPG file from the site. See an example below.

- Lemme Tweet That For You (http://lemmetweetthatforyou.com):
This tool is used to fabricate an embeddable and sharable fake tweet with a customizable username, body text, and number of RTs and favorites. Simulator.com also has a tool to create a fake tweet and download it as a JPG image file.

- FakePhoneText (http://www.fakephonetext.com/):
This tool is used to create and download a image of fake iPhone message conversation. You can set the name and content of the messages, as well also the cell network, time, type of connection (i.e. 3G, WIFI) and battery status. There is also another text message generator called iOS7 Text.

7. Fake websites
It may look real, but this wasn’t the authentic New York Post website. It was created to raise awareness about climate change. It’s relatively easy to copy a website and set it up on a different web address — and to fool people in the process. That was what Wikileaks did when it set up a fake copy of The New York Times’ website in order to promote an equally fake op-ed by columnist Bill Keller:
The differences were subtle, and even some New York Times journalists were fooled.
Tip: Check the URL, and search on different search engines to see if the URL matches with the top hits for that property. If unsure about a URL, perform a Whois search to see who owns the domain, and when it was first registered.